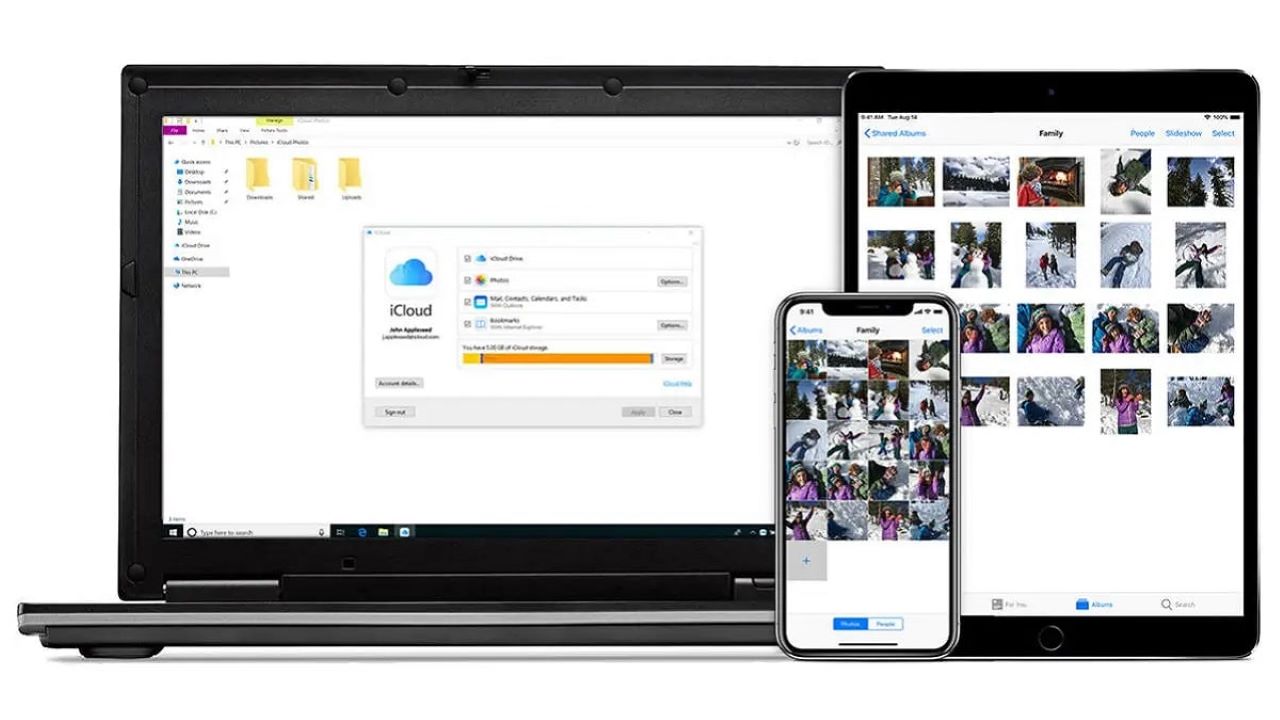
It is recent news, and we have also talked about it on these pages, that Apple’s cloud service has been subject to corruption (out of control alteration) of some users’ data. Specifically, a subset of users who used the software iCloud is a Windows system has reported corrupt video files and to have access to images of strangers.
It must immediately be said that while for the videos there are testimonials on the Internet, for extraneous photos there were only reports on social media. So, with a cool head, we still have to understand what really happened. More, Apple hasn’t commented on it yet. This means that in Cupertino they are still doing their checks.
What we can do, with these few elements, is try to sort things out to understand what the actual extent of the problem could be. Let’s try it together.
The operation of cloud services
Every service that we today call jargonally “in the cloud” supports its operation on a well-known paradigm: that of modello client-server. In un sistema client-server there are two actors involved: one requesting a service and the other providing it. The vast majority of services of The internet works like this.
In the case we’re looking at, they simplify a bit, on the one hand there is us with your phone or PC that we ask to be able to store data or to do a job and on the other is a data center with large computing and data storage capacities.
Data corruption in cloud
The question we are asking ourselves is simple: can there be data corruption in cloud?
The answer, sadly, is and.
Furthermore, it is not said that it can only happen to Apple. The speech we are about to make it applies to any cloud service. So, it could also happen to Google, Amazon, Microsoft, DropBox … and the list is very long. And most importantly, there are precedents.
But there is one important thing to keep in mind: it’s nearly impossible for data to become corrupted while sitting in a storage system. Just as it is almost impossible for a file to become corrupted while it is on the hard disk, the same is true when we entrust it to a data center. We say almost impossible because hardware failures cannot be predictedbut datacenters are expressly designed to make the event extremely unlikely.
However, data can become corrupted during their management. This is equivalent to saying three moments: when sending, transmitting and receiving. This means that, in case of an error, the responsibility could be of the software who handled the information or of the network.
Networks, after fifty years of evolution, are able to give us anvery high reliability. Modern transmission technologies make almost impossible for the data to be altered during their transmission. Even if it happens, they are done multiple integrity checks to request retransmission.
So, in case of data corruption, it remains as the only real suspect is the software.
User-side corruption
There may be a bug in the software we use to send data to the data center. Simply, the information sent does not correspond to what is present on our hard disk; there may be several different bytes, or it may be incomplete.
Therefore, if we admit the existence of a bug nel software iCloud per Windows, this explains why some videos on the cloud are corrupted. However, can not explain how it is possible that some users see photos that are not theirs. We may send corrupted data or send it in partial form; but we cannot create images out of thin air.
Data center corruption

Let us then assume that the bug is in the software used by the data center to store and access our data.
In this case it can be explained why the videos are corrupted and we see photos of others. The information stored in the data center is not the same as that received over the network and we are mistakenly given access to data that is not ours.
Too bad that this cannot explain why the reports only concern Windows. If the data center sends wrong data to users, then Apple devices should be affected as well. But that hasn’t been reported by anyone.
The third hypothesis
In reality, there is no third hypothesis; or better, it is not possible to make only one. The elements involved are many, and not all of them are known to us. It might even be there a bug in data center software that only triggers under certain conditions user side; using Windows could be one of these conditions. However, this last hypothesis opens up to slightly worrying scenarios. It cannot be excluded, in fact, that someone could understand, by analyzing the behavior of iCloud on Windows, how to activate and check the bug in the data center software. If so, it is difficult to predict what data this person would have access to.
To conclude, we would like to say that there could also be data corruption in the cloud, although we have not been able to find overwhelming evidence on the net, especially on the part of the photos. For this reason it is very important to wait for an official position from Apple which, we are convinced, is the first to want to understand what is happening.














Leave a Reply
View Comments